Please don't fall for any job/grants/SaaS/Software related scams. For any query or concerns please reach to us directly at +65 6834 3026 or WhatsApp at +65-8910 8216

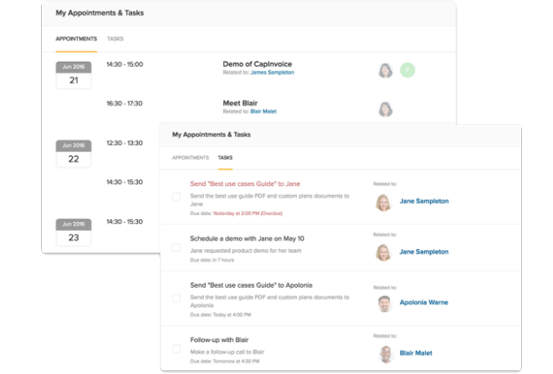
Providing users with the resources they need just-in-time is a necessity of any management software. Access permissions and security rights are a part of this, especially for companies with access to external apps.
Employees with varied responsibilities and job positions increasingly utilize external business solutions to perform their duties in today’s workplace. The identity and access management module help manage this by offering a single page to handle user identities and access rights.
Allowing you to control access to sensitive equipment and keep a track of who is creating and implementing changes in the system.
Managing users provides the most important advantage of all: asset safety. You may wish to restrict access to specific settings to prevent less-experienced users from making changes into the system.

Incorporating Employer Identification Number (PIN) to the asset reservation system Automates a big part of the operations. The system uses third-party scanning software to scan employee IDs. This increases efficiency, decreases human error, and generates a solid paper trail.
Pre-purchase or delivery, it’s easy to check a customer’s particulars; which is of a significant concern when transferring regulated products, such. Your client’s data is secured and processed in a safe and secure manner.
Our password policy is a collection of predefined rules for controlling, and managing passwords for users of the system. If necessary, you may set up password policy restrictions according to your company’s regulations.
A company’s or an organization’s password policy is determined at the corporate level and we are open to incorporating it into our software.
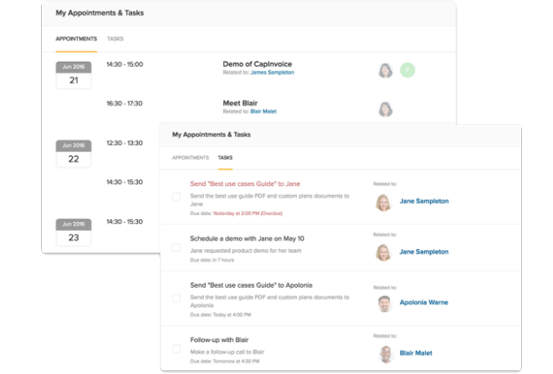

By utilizing the Genic Access Management’s role customization feature, you can configure a whole new user role from the scratch and assign it to various users according to your own preferences. When creating custom roles, multiple controls can be enforced as an extra security step.
Don’t know what the Genic Assets Management System offers for your business? Get a Demo to explore amazing Asset Management System features. Connect with us to Book a Demo!
Book a Demo